Distinguishing attack simulations from the real thing
In an era marked by the omnipresence of digital technologies and the relentless advancement of cyber threats, organizations face an ongoing battle to safeguard their digital environment. Although red and blue team exercises have long served as cornerstones in evaluating organizational defenses, their reliance on manual processes poses significant constraints [1]. Led by seasoned security professionals, these tests offer invaluable insights into security readiness but can be marred by their resource-intensive and infrequent testing cycles. The gaps between assessments leave organizations open to undetected vulnerabilities, compromising the true state of their security environment. In response to the ever-changing threat landscape, organizations are adopting a proactive stance towards cyber security to fortify their defenses.
At the forefront, these efforts tend to revolve around simulated attacks, a process designed to test an organization's security posture against both known and emerging threats in a safe and controlled environment [2]. These meticulously orchestrated simulations imitate the tactics, techniques, and procedures (TTPs) employed by actual adversaries and provide organizations with invaluable insights into their security resilience and vulnerabilities. By immersing themselves in simulated attack scenarios, security teams can proactively probe for vulnerabilities, adopt a more aggressive defense posture, and stay ahead of evolving cyber threats.
Distinguishing between simulated malware observations and authentic malware activities stands as a critical imperative for organizations bolstering their cyber defenses. While simulated platforms offer controlled scenarios for testing known attack patterns, Darktrace’s Self-Learning AI can detect known and unknown threats, identify zero-day threats, and previously unseen malware variants, including attack simulations. Whereas simulated platforms focus on specific known attack vectors, Darktrace DETECT™ and Darktrace RESPOND™ can identify and contain both known and unknown threats across the entire attack surface, providing unparalleled protection of the cyber estate.
Darktrace’s Coverage of Simulated Attacks
In January 2024, the Darktrace Security Operations Center (SOC) received a high volume of alerts relating to an unspecified malware strain that was affecting multiple customers across the fleet, raising concerns, and prompting the Darktrace Analyst team to swiftly investigate the multitude of incident. Initially, these activities were identified as malicious, exhibiting striking resemblance to the characteristics of Remcos, a sophisticated remote access trojan (RAT) that can be used to fully control and monitor any Windows computer from XP and onwards [3]. However, further investigation revealed that these activities were intricately linked to a simulated malware provider.
This discovery underscores a pivotal insight into Darktrace’s capabilities. To this point, leveraging advanced AI, Darktrace operates with a sophisticated framework that extends beyond conventional threat detection. By analyzing network behavior and anomalies, Darktrace not only discerns between simulated threats, such as those orchestrated by breach and attack simulation platforms and genuine malicious activities but can also autonomously respond to these threats with RESPOND. This showcases Darktrace’s advanced capabilities in effectively mitigating cyber threats.
Attack Simulation Process: Initial Access and Intrusion
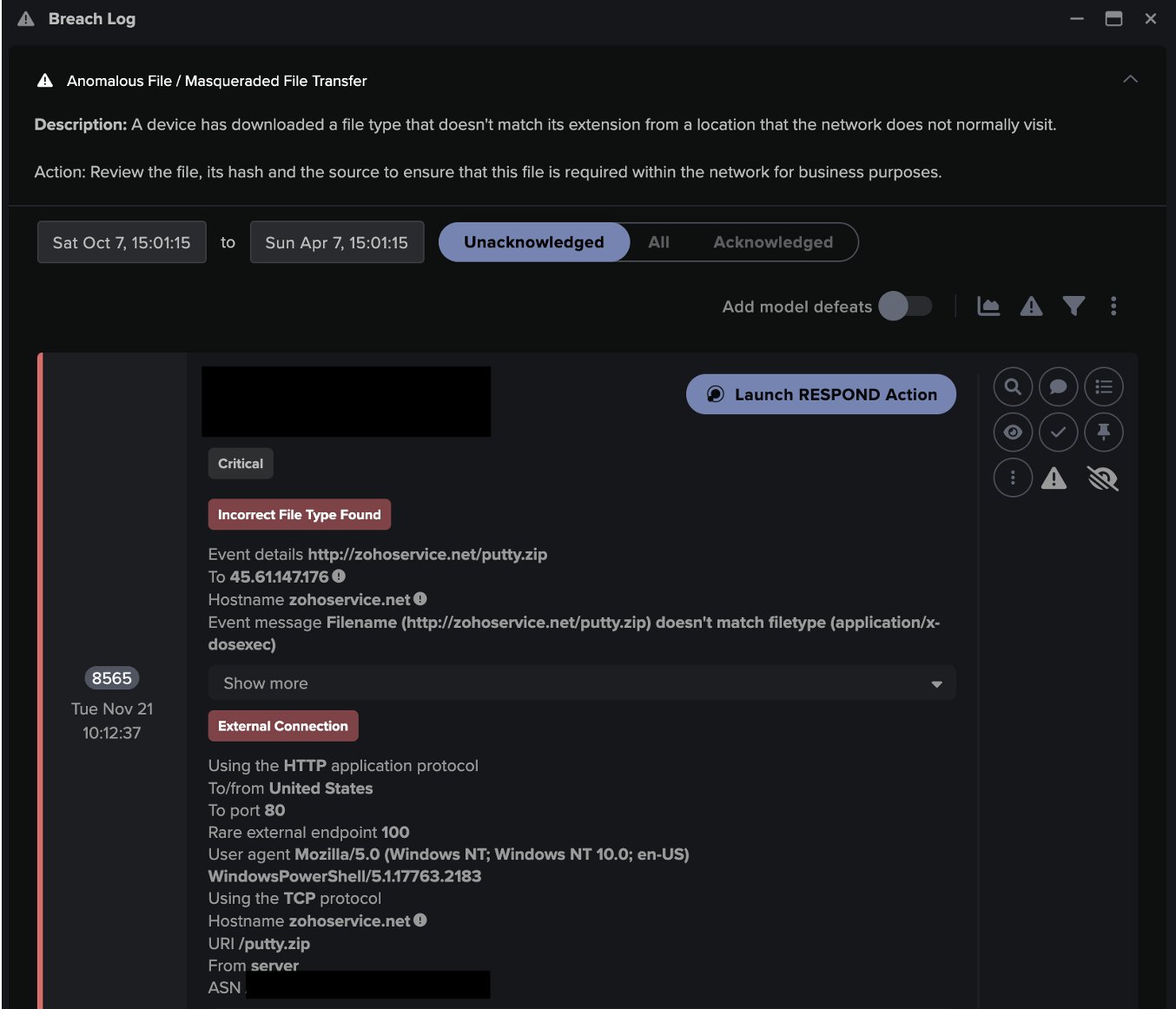
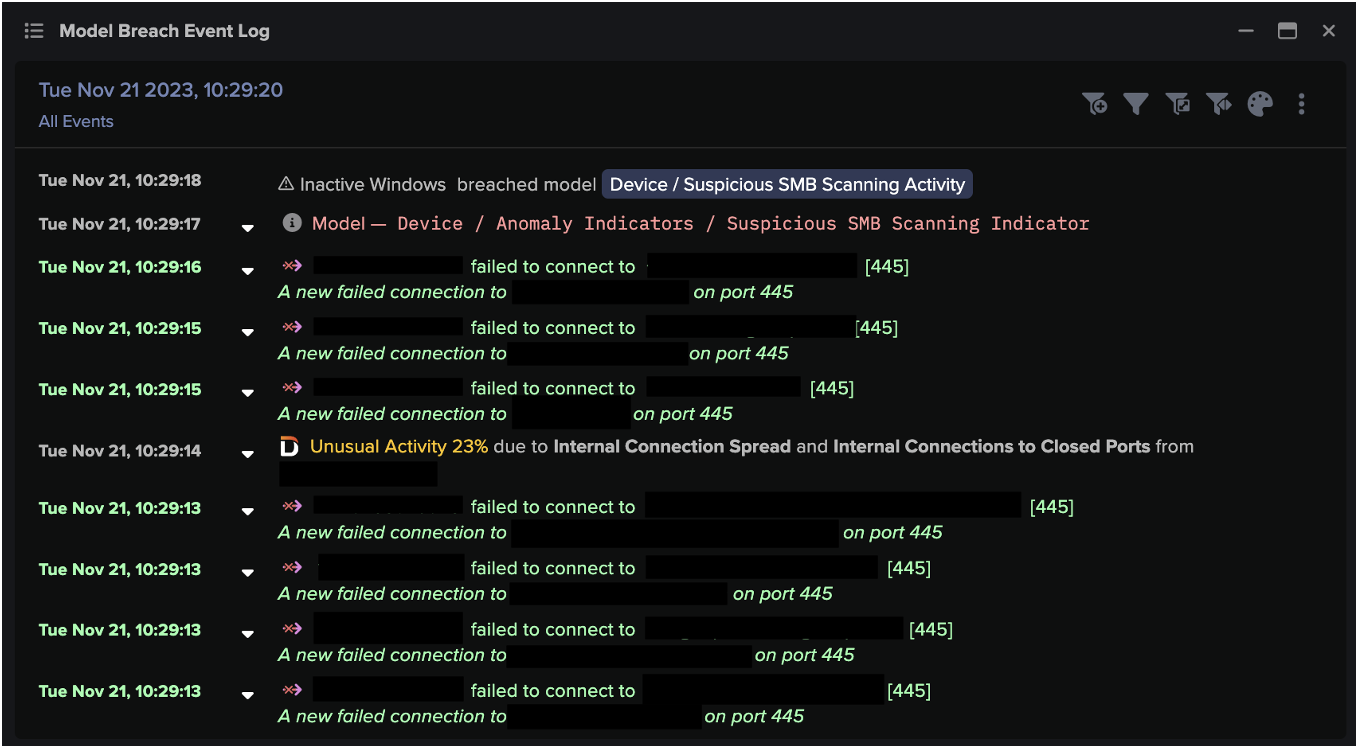
Darktrace initially observed devices breaching several DETECT models relating to the hostname “new-tech-savvy[.]com”, an endpoint that was flagged as malicious by multiple open-source intelligence (OSINT) vendors [4].
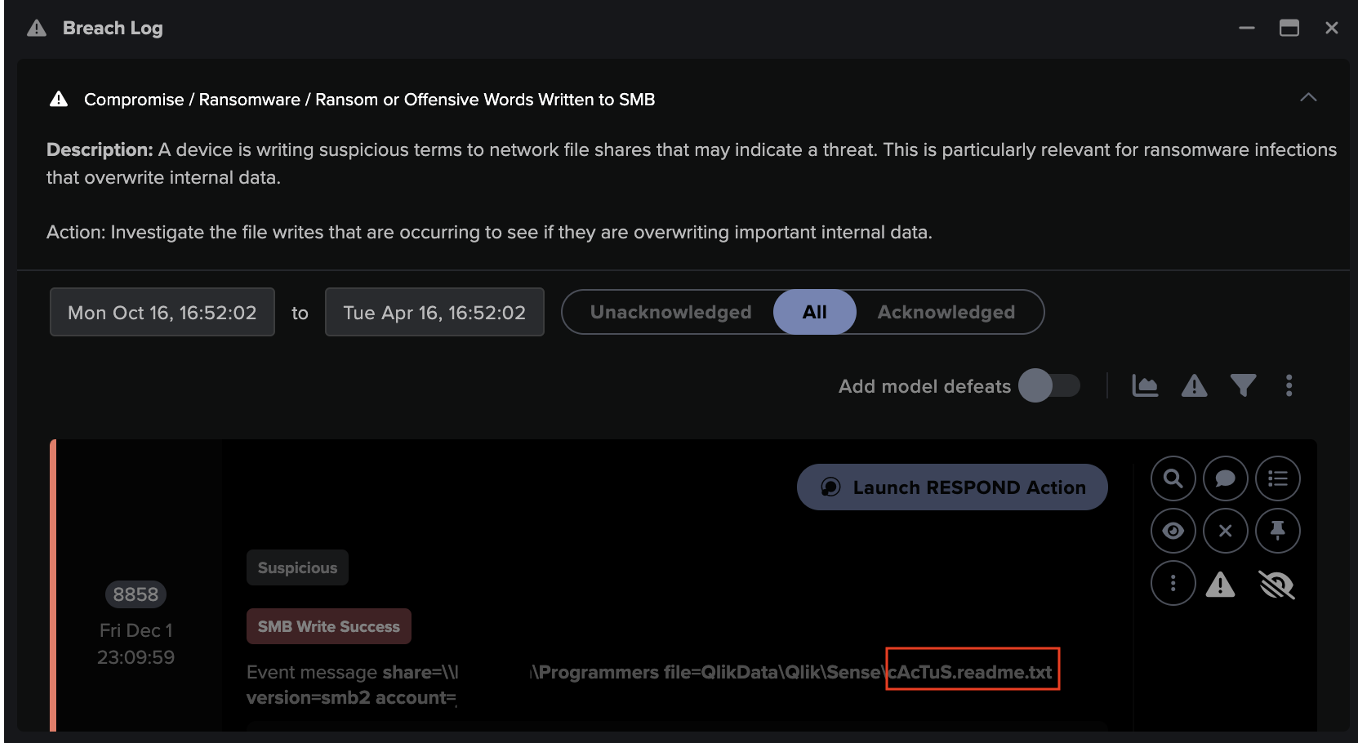
In addition, multiple HTML Application (HTA) file downloads were observed from the malicious endpoint, “new-tech-savvy[.]com/5[.]hta”. HTA files are often seen as part of the UAC-0050 campaign, known for its cyber-attacks against Ukrainian targets, which tends to leverage the Remcos RAT with advanced evasion techniques [5] [6]. Such files are often critical components of a malware operation, serving as conduits for the deployment of malicious payloads onto a compromised system. Often, within the HTA file resides a VBScript which, upon execution, triggers a PowerShell script. This PowerShell script is designed to facilitate the download of a malicious payload, namely “word_update.exe”, from a remote server. Upon successful execution, “word_update.exe” is launched, invoking cmd.exe and initiating the sharing of malicious data. This process results in the execution of explorer.exe, with the malicious RemcosRAT concealed within the memory of explorer.exe. [7].
As the customers were subscribed to Darktrace’s Proactive Threat Notification (PTN) service, an Enhanced Monitoring model was breached upon detection of the malicious HTA file. Enhanced Monitoring models are high-fidelity DETECT models designed to identify activity likely to be indicative of compromise. These PTN alerts were swiftly investigated by Darktrace’s round the clock SOC team.
Following this successful detection, Darktrace RESPOND took immediate action by autonomously blocking connections to the malicious endpoint, effectively preventing additional download attempts. Similar activity may be seen in the case of a legitimate malware attack; however, in this instance, the hostname associated with the download confirmed the detected malicious activity was the result of an attack simulation.

'


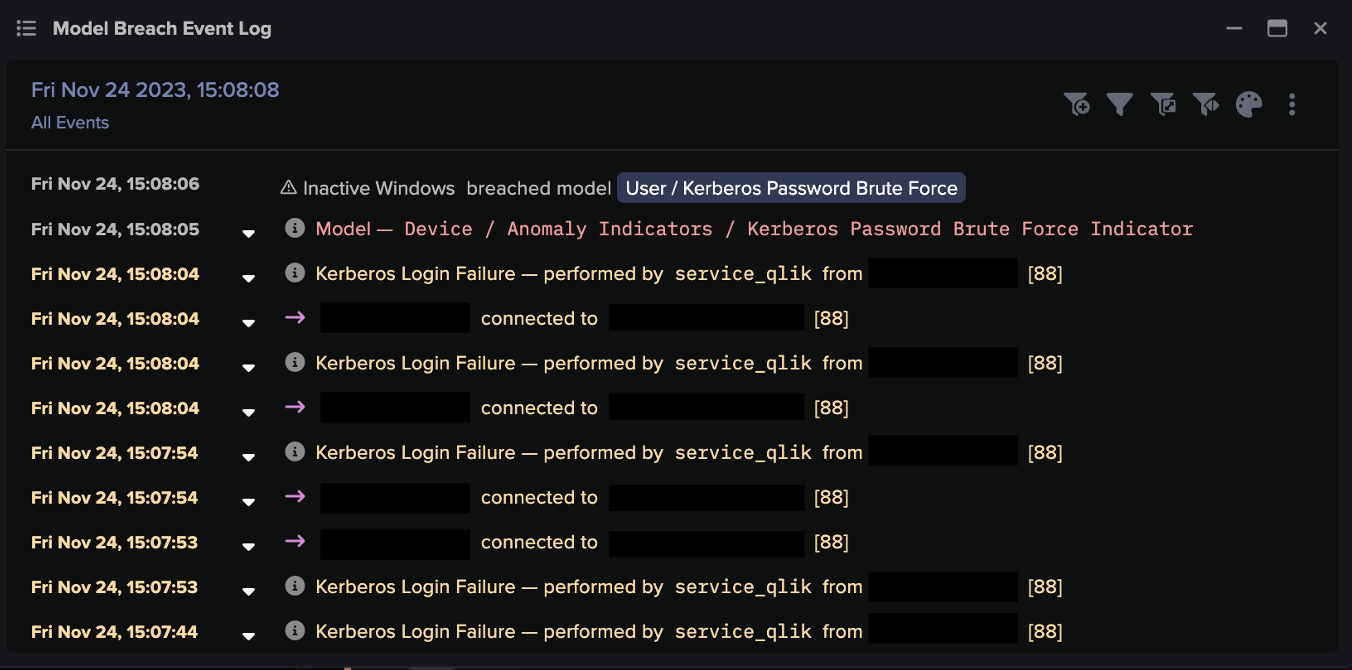
In other cases, Darktrace observed SSL and HTTP connections also attributed to the same simulated malware provider, highlighting Darktrace’s capability to distinguish between legitimate and simulated malware attack activity.



Upon detection of the malicious activity occurring within affected customer networks, Darktrace’s Cyber AI Analyst™ investigated and correlated the events at machine speed. Figure 8 illustrates the synopsis and additional technical information that AI Analyst generated on one customer’s environment, detailing that over 220 HTTP queries to 18 different endpoints for a single device were seen. The investigation process can also be seen in the screenshot, showcasing Darktrace’s ability to provide ‘explainable AI’ detail. AI Analyst was able to autonomously search for all HTTP connections made by the breach device and identified a single suspicious software agent making one HTTP request to the endpoint, 45.95.147[.]236.
Furthermore, the malicious endpoints, 45.95.147[.]236, previously observed in SSH attacks using brute-force or stolen credentials, and “tangible-drink.surge[.]sh”, associated with the Androxgh0st malware [8] [9] [10], were detected to have been requested by another device.
This highlights Darktrace’s ability to link and correlate seemingly separate events occurring on different devices, which could indicate a malicious attack spreading across the network. AI Analyst was also able to identify a username associated with the simulated malware prior to the activity through Kerberos Authentication Service (AS) requests. The device in question was also tagged as a ‘Security Device’ – such tags provide human analysts with valuable context about expected device activity, and in this case, the tag corroborates with the testing activity seen. This exemplifies how Darktrace’s Cyber AI Analyst takes on the labor-intensive task of analyzing thousands of connections to hundreds of endpoints at a rapid pace, then compiling results into a single pane that provides customer security teams with the information needed to evaluate activities observed on a device.
All in all, this demonstrates how Darktrace’s Self-Learning AI is capable of offering an unparalleled level of awareness and visibility over any anomalous and potentially malicious behavior on the network, saving security teams and administrators a great deal of time.

Conclusion
Simulated cyber-attacks represent the ever-present challenge of testing and validating security defenses, while the threat of legitimate compromise exemplifies the constant risk of cyber threats in today’s digital landscape. Darktrace emerges as the solution to this conflict, offering real-time detection and response capabilities that identify and mitigate simulated and authentic threats alike.
While simulations are crafted to mimic legitimate threats within predefined parameters and controlled environments, the capabilities of Darktrace DETECT transcend these limitations. Even in scenarios where intent is not malicious, Darktrace’s ability to identify anomalies and raise alerts remains unparalleled. Moreover, Darktrace’s AI Analyst and autonomous response technology, RESPOND, underscore Darktrace’s indispensable role in safeguarding organizations against emerging threats.
Credit to Priya Thapa, Cyber Analyst, Tiana Kelly, Cyber Analyst & Analyst Team Lead
Appendices
Model Breaches
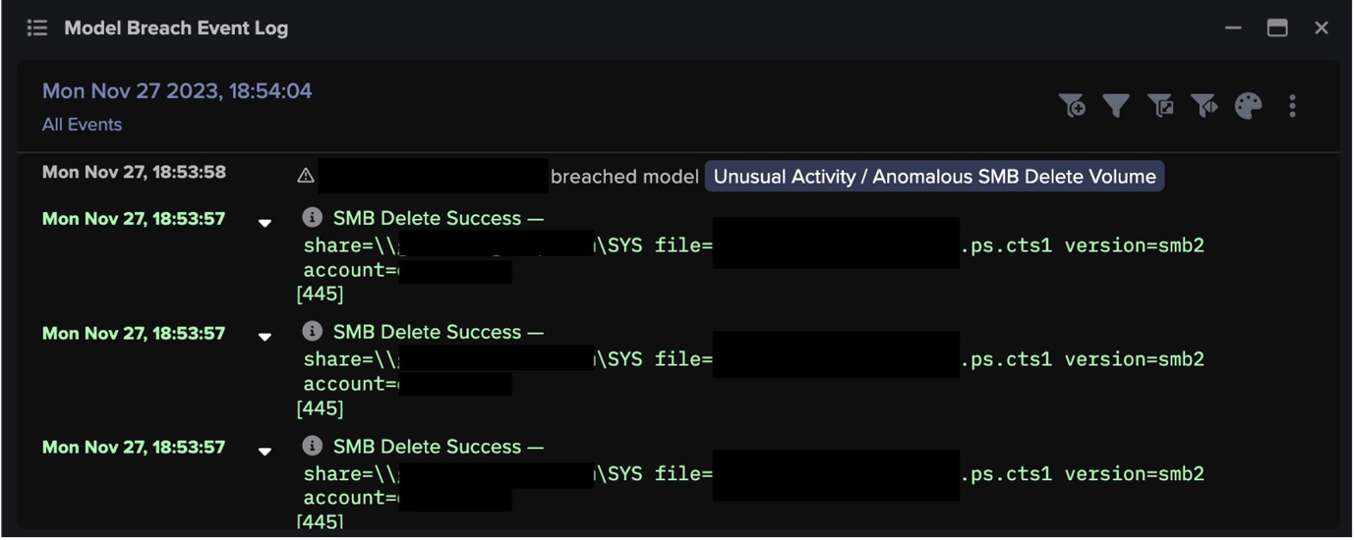
Darktrace DETECT Model Breach Coverage
Anomalous File / Incoming HTA File
Anomalous Connection / Low and Slow Exfiltration
Darktrace RESPOND Model Breach Coverage
§ Antigena / Network/ External Threat/ Antigena File then New Outbound Block
Cyber AI Analyst Incidents
• Possible HTTP Command and Control
• Suspicious File Download
List of IoCs
IP Address
38.52.220[.]2 - Malicious Endpoint
46.249.58[.]40 - Malicious Endpoint
45.95.147[.]236 - Malicious Endpoint
Hostname
tangible-drink.surge[.]sh - Malicious Endpoint
new-tech-savvy[.]com - Malicious Endpoint
References
1. https://xmcyber.com/glossary/what-are-breach-and-attack-simulations/
2. https://www.picussecurity.com/resource/glossary/what-is-an-attack-simulation
4. https://www.virustotal.com/gui/url/c145cf7010545791602e9585f447347c75e5f19a0850a24e12a89325ded88735
5. https://www.virustotal.com/gui/url/7afd19e5696570851e6413d08b6f0c8bd42f4b5a19d1e1094e0d1eb4d2e62ce5
6. https://thehackernews.com/2024/01/uac-0050-group-using-new-phishing.html
7. https://www.uptycs.com/blog/remcos-rat-uac-0500-pipe-method
8. https://www.virustotal.com/gui/ip-address/45.95.147.236/community
9. https://www.virustotal.com/gui/domain/tangible-drink.surge.sh/community
10. https://www.cisa.gov/news-events/cybersecurity-advisories/aa24-016a































![Cyber AI Analyst Incident Log showing the offending device making over 1,000 connections to the suspicious hostname “zohoservice[.]net” over port 8383, within a specific period.](https://assets-global.website-files.com/626ff4d25aca2edf4325ff97/662971c1cf09890fd46729a1_Screenshot%202024-04-24%20at%201.55.10%20PM.png)